Keeping your business and your people safe online doesn’t have to be complicated.
At Cyber Wardens, we believe in making cyber security simple and that means breaking down the jargon, so you don’t have to. Read on for what you need to know to better understand how to keep your digital doors locked from cyber criminals.
Business Email Compromise (BEC)
Cloud computing (‘the cloud’)
The cloud is a global network of remote high-powered computers (called servers) that store your important information like business records, documents and photos. It is like a giant safe that can store trillions of files safely, and make sure that even if those files are accidentally or maliciously deleted on your local computer you can still access them in the cloud (the giant safe) anywhere in the world as long as you have an internet connection. Extra security features on the cloud ensure your information can be backed-up so that you don’t lose important files. Cloud service providers that offer this kind of ‘giant safe’ include Dropbox, Google Drive and Microsoft OneDrive.
Data
Any information or business files that you store digitally, similar to the sorts of documents you would keep in a physical safe. This could be information about your customers, such as their contact details, purchase history and any of their communication with your business. Data includes the kind of information your business can get through email interactions, mailing lists, social media accounts as well as your accounting and payments process. Data is valuable and very attractive for cyber criminals.


Data breach
A digital break-in where information is stolen or exposed. This can include your personal information, customer details, passwords and logins, or credit card details. A data breach is the equivalent of a criminal breaking into your physical business and stealing sensitive documents or whole computers.
Digital footprint
The information people leave behind when they use the internet or digital devices. It is similar to the physical footprints we leave behind when we’re walking through a muddy track. These footprints are also left online when we go about our day to day business.
Encryption
This is essentially a process that scrambles your data so that it can’t be read by cyber criminals unless they have the key or password to unscramble it. Encryption is similar to mixing up the pieces of a very large puzzle so that it becomes impossible for anyone to solve, unless they have the key to putting it back together. It turns information into a secret code which can only be decoded by people who are allowed to see it, so it protects your sensitive business files.
Firewall
The digital version of a giant wall with barbed wire meant to keep cyber criminals out of your computer and business network. A firewall can help prevent a digital break in by making it harder for cyber criminals to access your sensitive information.


Government agency: Australian Cyber Security Centre (ACSC)
Australian Government agency whose role it is to keep Australians safe and secure online. The ACSC provides advice and information about how to protect yourself and your business from cyber risks. It also monitors, investigates and develops solutions to cyber security threats around the world.
Impersonation attacks and scams
A scam where cyber criminals claim to be from a trusted organisation (eg. a bank, a telco, Australia Post) to try to convince you to make a payment or hand over important information.
Malicious software or malware
Any computer program, or software, that infects your computer system and steals protected data, deletes documents or adds software that you didn’t approve. Malware can be downloaded accidentally by clicking on a malicious link. Viruses, trojans and worms are all kinds of malware.
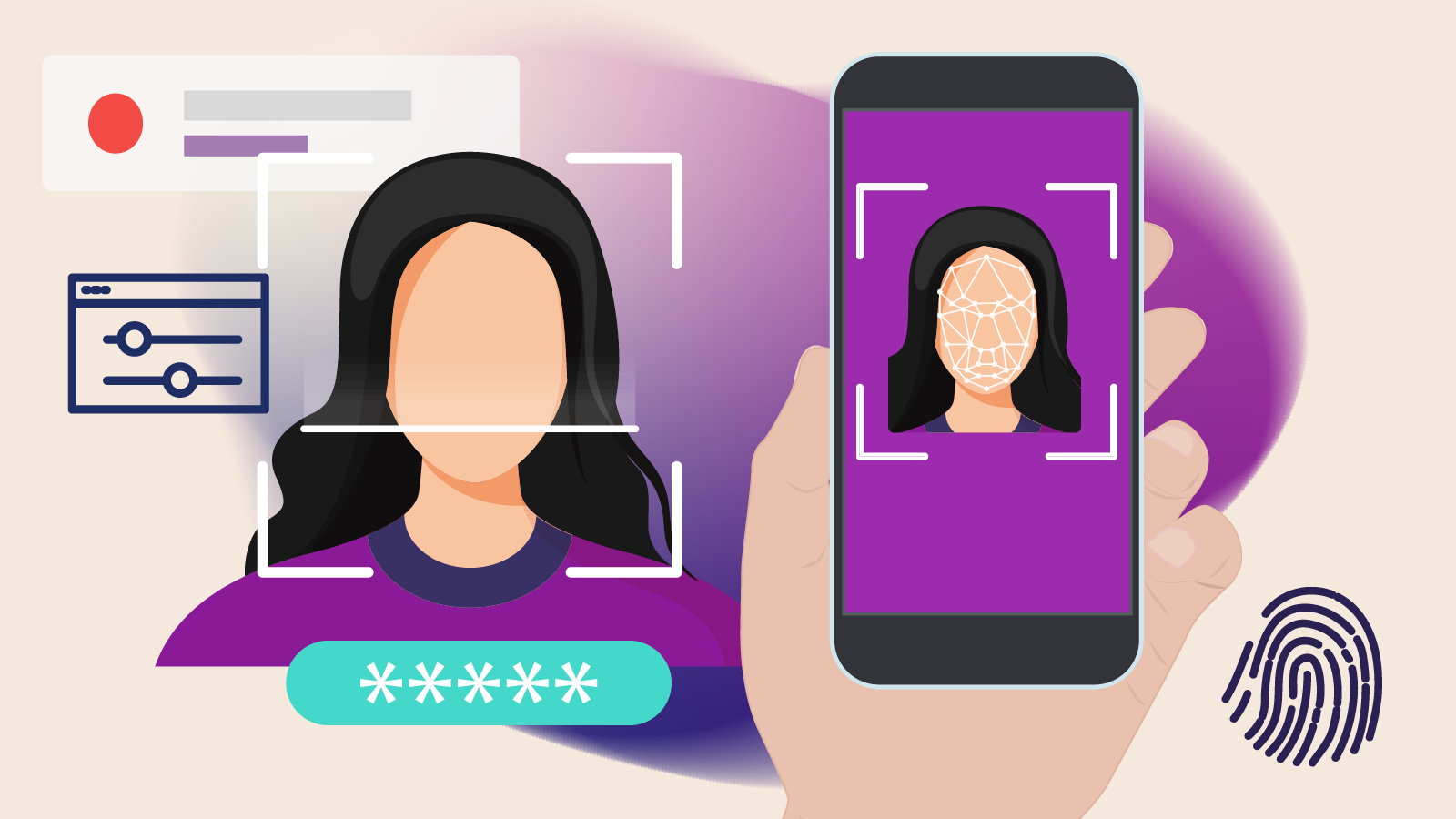
Multi-Factor Authentication (MFA)
The cyber equivalent of locking the front door of your business and turning on the alarm. MFA essentially means anyone who wants to access your account or system has to go through more security hurdles to do so. This involves unlocking the front door first (by providing the right password) and then turning off the alarm system (by either answering a secret question, entering a code sent to your email or scanning a fingerprint). This helps prevent cyber criminals accessing your personal information even if your password is compromised.
Phishing
A type of crime where cyber criminals send emails asking you to provide sensitive information or download something harmful onto your computer that allows them to gain access to it. They might ask for your bank details, encourage you to open a dangerous attachment or visit a fake website. They are essentially fishing for any information that will allow them to engage in criminal behaviour.

These sorts of emails can be sent to multiple people at once. When cyber criminals target a specific group, it’s called ‘spear phishing’.

Scam
When cyber criminals try to trick people and businesses into handing over personal details, installing malware, paying money or causing damage. They can do this through your email, text messages, phone calls, which allow criminals to pretend to be from a legitimate company.
Instead of finding an unlocked window to the warehouse or forcing a break-in to your systems, scammers trick people into handing over their money willingly: You think you’re making a legit transaction or investment; they’re gleefully stealing your money.
Social Engineering
A type of cyber crime that involves trying to manipulate and trick people into breaking security procedures and handing over sensitive information. These attacks are common because it is often easier for a cyber criminal to get people to hand over details rather than ‘hack’ a system themselves, which is similar to picking the lock of a physical front door.
Spyware
Software that collects information on your computer activity without your consent. Like a spy tracking someone’s day to day activities, it’ll watch every move you make on your computer, including entering passwords and important information. Spyware can be installed on your system by a cyber criminal themselves or as part of other software you download without your knowledge.
Virus
A type of malware that can replicate itself and spread to other computers or networks, similar to a physical virus that infects the body. This can badly impact a business by corrupting the computer system and files, destroying important data, stealing passwords, spying on activity and spamming email contacts.